Archive
This post is archived and may contain outdated information. It has been set to 'noindex' and should stop showing up in search results.
This post is archived and may contain outdated information. It has been set to 'noindex' and should stop showing up in search results.
Recover from and Protect Against Ransomware Virus Attacks
May 15, 2017WindowsComments (0)
Ransomware is a type of malware and virus that encrypts your personal files and seeks a payment in order to gain access to the decryption key. It targets documents, pictures, spreadsheets, and other common files. The payment is usually requested via bitcoin.
If the computer that is infected by ransomware is currently powered on and not in Safe Mode, turn it off immediately using the power button on the front (hold it for several seconds until it shuts down). You'll want to perform any recovery steps from an uninfected computer or from Windows Safe Mode.
Any files the ransomware got its hands on before you shut down will now be encrypted. Trying to access them in Word, Excel, or any other program will give an error message or display unintelligible characters. Here are some options for recovering these files:
Decryption Tools
The first method you can try is a decryption program. The project No More Ransomware has a tool that you can use to try and identify the type of ransomware, and provide a decryption tool for it. Please refer to that website for instructions on using it (www.nomoreransom.org).
File Backup
Often times the ransomware's encryption is too strong to decrypt. Hopefully you've been making regular backups of your personal files. If you have, then prior to restoring your files be sure to clean the infected computer using a good malware program like Malwarebytes (www.malwarebytes.com) from Windows Safe Mode. For a guide on updating and using Malwarebytes from Safe Mode (without Internet), see here.
Recover Deleted Data
It's possible you may be able to recover your original files using a program like EaseUS Data Recovery (www.easeus.com). When a file is deleted on Windows, usually the bytes that comprise that file are not actually deleted. The file is just hidden until the data is overwritten.
A smart ransomware program will make this not possible, but if you're running out of options, it's something to try. There are many companies that offer data recovery services that use programs like these (and even better ones).
Paying the Ransom
There is no guarantee that you'll get your files back if you pay the ransom. It is not recommended to do so, although in the worst case scenario it is an option to consider. I won't cover that here as I don't think it's a good solution. Search the Internet for advice and recommendations on paying ransomware.
Protecting from ransomware is the same as protecting from any virus, malware, or other computer calamity. It involves changing your computing habits to avoid contracting bad software, and keeping regular (daily) backups of your important files.
Bad Email Habits
Read these guidelines to learn how to properly check your email. Email from what appears to be friends and family is the number one avenue for attackers to get malicious software onto your computer.
Using a Standard Windows User
I recommend adding a password to your Administrator Windows user, and then creating a Standard user that is your daily driver.
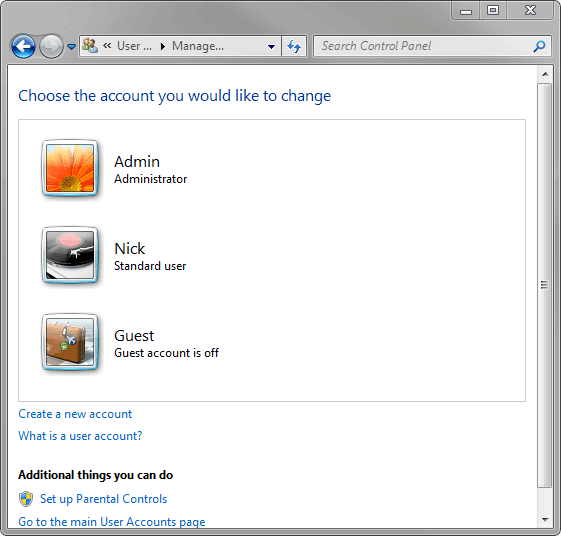
When using the Standard user account, any system changes, such as a program install, will require that you enter your Admin password in a dialog popup. This will make you think twice before installing something or changing a setting, but still allow you to do so without too much inconvenience.
Daily Backups
Use a program like Duplicati (www.duplicati.com) to keep a daily backup of your important files. I recommend using it with Google Drive, and setting the daily schedule to be a time when your computer is on. Your backups will be updated and saved automatically to your Google Drive account, and it will happen in the background with very little impact on your system.
What about Antivirus Programs?
You're free to use an antivirus program in conjunction with the above recommendations. Just understand that antivirus programs aren't perfect. They don't allow you to do whatever you want and be safe. You must still be a smart computer user.
Emergency Instructions
If the computer that is infected by ransomware is currently powered on and not in Safe Mode, turn it off immediately using the power button on the front (hold it for several seconds until it shuts down). You'll want to perform any recovery steps from an uninfected computer or from Windows Safe Mode.
Recovering from Ransomware
Any files the ransomware got its hands on before you shut down will now be encrypted. Trying to access them in Word, Excel, or any other program will give an error message or display unintelligible characters. Here are some options for recovering these files:
Decryption Tools
The first method you can try is a decryption program. The project No More Ransomware has a tool that you can use to try and identify the type of ransomware, and provide a decryption tool for it. Please refer to that website for instructions on using it (www.nomoreransom.org).
File Backup
Often times the ransomware's encryption is too strong to decrypt. Hopefully you've been making regular backups of your personal files. If you have, then prior to restoring your files be sure to clean the infected computer using a good malware program like Malwarebytes (www.malwarebytes.com) from Windows Safe Mode. For a guide on updating and using Malwarebytes from Safe Mode (without Internet), see here.
Recover Deleted Data
It's possible you may be able to recover your original files using a program like EaseUS Data Recovery (www.easeus.com). When a file is deleted on Windows, usually the bytes that comprise that file are not actually deleted. The file is just hidden until the data is overwritten.
A smart ransomware program will make this not possible, but if you're running out of options, it's something to try. There are many companies that offer data recovery services that use programs like these (and even better ones).
Paying the Ransom
There is no guarantee that you'll get your files back if you pay the ransom. It is not recommended to do so, although in the worst case scenario it is an option to consider. I won't cover that here as I don't think it's a good solution. Search the Internet for advice and recommendations on paying ransomware.
Protecting From Ransomware
Protecting from ransomware is the same as protecting from any virus, malware, or other computer calamity. It involves changing your computing habits to avoid contracting bad software, and keeping regular (daily) backups of your important files.
Bad Email Habits
Read these guidelines to learn how to properly check your email. Email from what appears to be friends and family is the number one avenue for attackers to get malicious software onto your computer.
Using a Standard Windows User
I recommend adding a password to your Administrator Windows user, and then creating a Standard user that is your daily driver.
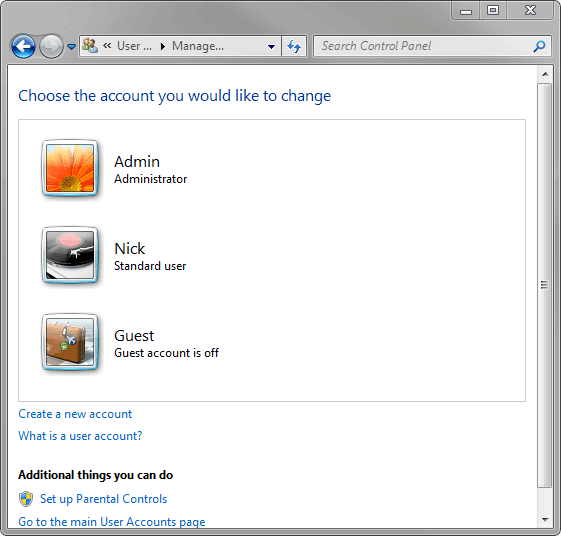
When using the Standard user account, any system changes, such as a program install, will require that you enter your Admin password in a dialog popup. This will make you think twice before installing something or changing a setting, but still allow you to do so without too much inconvenience.
Daily Backups
Use a program like Duplicati (www.duplicati.com) to keep a daily backup of your important files. I recommend using it with Google Drive, and setting the daily schedule to be a time when your computer is on. Your backups will be updated and saved automatically to your Google Drive account, and it will happen in the background with very little impact on your system.
What about Antivirus Programs?
You're free to use an antivirus program in conjunction with the above recommendations. Just understand that antivirus programs aren't perfect. They don't allow you to do whatever you want and be safe. You must still be a smart computer user.